Infrastructure & Network Operations.Controlled. Protected. Always Running.
Network Infrastructure Management
Your network is not a background utility. It is the operational backbone of your organization.
In the RedZone, your infrastructure is secure, stable, and accountable.
It supports expansion. It protects enterprise value. It withstands scrutiny.

Network Infrastructure Performance You Can Quantify
Effective network infrastructure is measured by stability, performance, and resilience. When infrastructure management services are structured correctly, systems operate efficiently and leadership has predictable outcomes.
RedZone does not operate as a commodity MSP. We manage mission-critical infrastructure where performance, compliance, and resilience are imperative.
With our managed network infrastructure services, you gain:
- Reduced downtime across critical systems
- Optimal network performance across locations
- Clean, documented, scalable environments
- Stronger access control and reduced attack surface
- Infrastructure that supports growth initiatives
Reactive Network Operations Create Exposure…
Many organizations believe their infrastructure is stable because it is running. In regulated environments, that assumption is dangerous.
RedZone addresses common weaknesses through structured, disciplined network infrastructure management.
❌ Fragmented network design with no long-term strategy
✅ Our managed network infrastructure is documented, standardized, and engineered to scale without rework.
❌ Fragmented network design with no long-term strategy
✅ Our managed network infrastructure is documented, standardized, and engineered to scale without rework.
❌ Fragmented network design with no long-term strategy
✅ Our managed network infrastructure is documented, standardized, and engineered to scale without rework.
Trusted by Organizations That Can’t Afford Risk
Trusted by Organizations That Can’t Afford Risk
“I want to thank you for supporting us last night with our emergency. You deployed your "A-Team" and it is refreshing to have a vendor respond with a sense of urgency and resourcefulness. Our IT manager said that RedZone was 'just awesome.'”
“When the NFL required every team in the league to do a Security Risk Assessment, we chose RedZone. Their Security Scoreboard gives my department all the technical information we need, while still displaying the data in a way our board can understand. It's unlike anything else on the market.”
Four Pillars. One Controlled Environment.
Your infrastructure posture determines your exposure.
We design secure architecture that establishes a controlled, well-structured foundation for managing your network.
- Stronger security posture across all infrastructure layers
- Standardized configurations across network devices
- Structured access control aligned to least-privilege principles
- Clean, documented, scalable environments
Resilience begins with reducing exposure.
We apply disciplined network hardening practices across firewalls, switches, wireless infrastructure, and perimeter systems.
- Reduced attack surface across network devices
- Greater infrastructure resilience during peak demand
- Controlled change management processes
- Minimized downtime caused by preventable misconfiguration
Intelligence comes from visibility.
We proactively monitor infrastructure using modern management tools that provide insight into performance, traffic behavior, and system health.
- Real time insight across cloud and data center environments
- Improved performance and optimal network performance
- Early identification of instability
- Infrastructure that operates efficiently under changing demand
Compliance depends on disciplined risk control.
Infrastructure components are regularly assessed, prioritized, and remediated based on risk severity and regulatory exposure.
- Reduced exposure windows for critical vulnerabilities
- Audit-ready documentation and reporting
- Structured remediation cycles
- Stronger regulatory alignment across regulated industries
Infrastructure for High-Responsibility Environments

Financial Services
Financial institutions depend on stable, secure infrastructure to maintain transaction integrity and regulatory standing.
We deliver reduced downtime, stronger access control, and continuous vulnerability management aligned to frameworks such as PCI-DSS, SOX, and FFIEC guidance. The outcome is predictable operations, audit readiness, and infrastructure that supports growth.

Healthcare & Dental
Healthcare providers operate under strict compliance requirements and cannot tolerate extended system outages.
We ensure optimal network performance across clinical systems, secure handling of protected health information, and documented environments that support HIPAA compliance. The result is stable operations, protected patient data, and minimized operational interruption.

Manufacturing
Manufacturers rely on connected systems and integrated supply chains. Infrastructure instability directly affects production timelines.
We strengthen infrastructure resilience across sites and facilities, ensuring network devices and core systems operate efficiently under demand. This improves performance across production systems and supports expansion without compromising operational control.
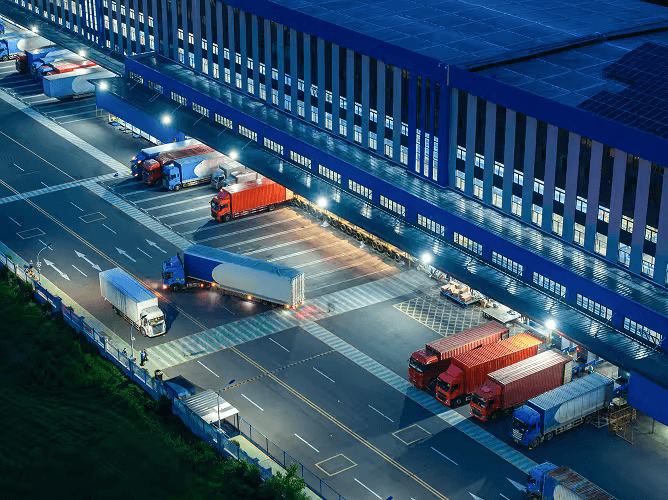
Logistics & Transportation
Logistics organizations depend on real time data flow between warehouses, fleet systems, and distribution centers.
Our managed network services deliver resilient connectivity, consistent performance across distributed environments, and structured network operations. The outcome is seamless coordination, reliable system availability, and infrastructure that supports time-sensitive operations.
Our technology partners




























RedZone: Turning Infrastructure Into an Asset
Security-Led
Every architectural decision strengthens your security posture and aligns to regulatory expectations. Exposure is identified early and addressed systematically.
AI-Native
We use modern, AI-native management tools to enhance visibility. Real time telemetry enables faster detection and measurable operational improvement.
Purpose-Built
We understand the expectations placed on highly regulated organizations. Our approach reflects the accountability these sectors require.
Infrastructure That Performs Under Pressure.
Take It As Red.
Most managed service providers operate as ticket processors. They respond to alerts, rotate tools, and measure success by volume.
RedZone operates differently.
We do not layer IT infrastructure and network management services onto unstable foundations. We assess, redesign where necessary, standardize configurations, and continuously evaluate performance.
Managed Network Infrastructure Services FAQ
Effective network infrastructure management starts with structured architecture and standardized configuration across all network devices. Best practices include documented network design, enforced access control policies, continuous vulnerability management, and real time monitoring using modern management tools.
Organizations should ensure their managed network infrastructure is proactively monitored, regularly assessed, and aligned to compliance requirements.
Improving IT infrastructure begins with a comprehensive assessment of your current network and infrastructure management model. Identify configuration inconsistencies, outdated management tools, access control weaknesses, and performance bottlenecks.
Adopting structured infrastructure management services that include secure architecture design, network hardening, monitoring and optimization, and continuous vulnerability management will improve performance and resilience.
Comprehensive managed network services typically include:
- Network design and architecture planning
- Configuration management across network devices
- Access control governance
- Monitoring and optimization in real time
- Vulnerability management and patch oversight
- Performance tuning across data center and cloud environments
- Incident response and minimizing downtime
Effective network infrastructure management services integrate these capabilities into a structured operating model.
Effective network and infrastructure management delivers measurable business outcomes.
It helps reduce downtime, improve performance, and ensure seamless connectivity across distributed environments. It strengthens compliance posture through documented controls and structured vulnerability management. It also improves operational efficiency by reducing reactive workload on internal IT teams.
For regulated organizations, managed network infrastructure provides stability that protects revenue, reputation, and audit readiness.