Cyber Exposure Has Consequences…
Cyber risks affect more than systems. They affect revenue, operations, compliance, and reputation.
- Uncontrolled access expands the attack surface
- Gaps in vulnerability management leave systems exposed
- Security tools operate in silos
- Incident response plans go untested
This results in avoidable exposure across critical information systems.
RedZone is the managed security service provider (MSSP) that mitigates both the risk and the impact.
Our objective is simple: Fewer successful breaches. Faster containment. Greater control.

In the RedZone, Security is Managed With Discipline
RedZone is not a generalist cybersecurity service provider. We operate as a security-led partner for regulated organizations where outcomes matter.
Our managed cybersecurity services are measured in operational performance and reduced exposure.
Our clients experience:
- Reduced breach probability through structured security measures and tracked exposure.
- Faster response when security incidents occur, reducing the impact and spread.
- Clear accountability through executive oversight and documented governance.
- Operational certainty as cyber risks are actively managed across posture, resilience, compliance, and intelligence.
Trusted by Organizations That Can’t Afford Risk
Trusted by Organizations That Can’t Afford Risk
“I want to thank you for supporting us last night with our emergency. You deployed your "A-Team" and it is refreshing to have a vendor respond with a sense of urgency and resourcefulness.”
“When the NFL required every team in the league to do a Security Risk Assessment, we chose RedZone. Their Security Scoreboard gives my department all the technical information we need, while still displaying the data in a way our board can understand.”
Your Attack Surface Is a Board Issue
RedZone translates cyber risk management into business exposure and financial impact. Reporting connects security posture to operational continuity, regulatory compliance, and fiduciary responsibility.
This gives leadership greater visibility into risk trends, control maturity, and incident readiness without being drawn into technical detail.
The result is informed oversight, structured governance, and documented accountability at board level.
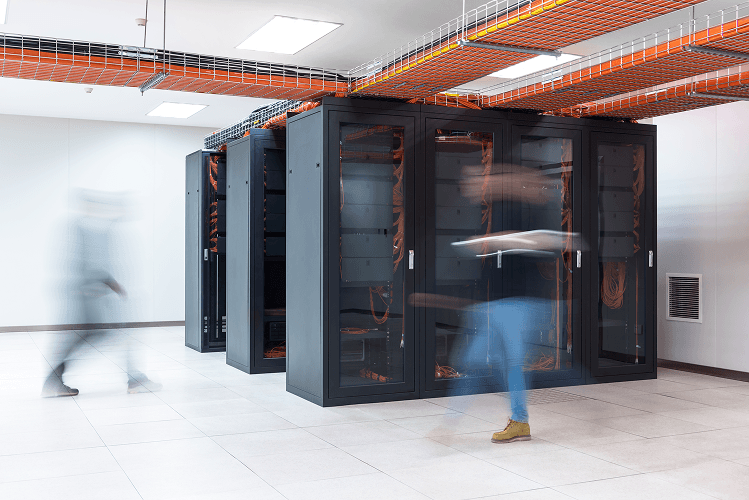
Unified Services. Measurable Reduction in Risk.
We structure cybersecurity risk management services across five integrated domains. Each service strengthens your security posture, reinforces resilience, sustains compliance, and sharpens operational intelligence.
The emphasis is always on measurable reduction of cyber risk and controlled business impact.
Our technology partners




























Our Approach
Specialist Focus. Regulated Strength.
Continuous Security Assessments
We benchmark controls against established standards, identify exposure across your attack surface, and map findings to business risk. This structured model keeps cybersecurity aligned to operations.
Embedded Compliance Management
Controls are documented, evidence is maintained, and reporting aligns to frameworks such as HIPAA, NIST, and PCI-DSS where applicable. Audits become structured reviews of maintained standards.
Executive-Level Strategic Enhancement
We support board reporting, risk modeling, and long-term security roadmap development. Cyber risk management is aligned to business strategy, growth plans, and regulatory obligations.
This is the End of Reactive Security
Cybersecurity risk management needs to be continuous, governed, and outcome-driven.
RedZone delivers managed cybersecurity services that reduce breach probability, accelerate response, and sustain regulatory compliance. We align cyber risk management to executive oversight and operational execution.
The result is measurable control across your attack surface, structured resilience across your infrastructure, and accountability at every level of the organization.
Your security is not left to chance. It is actively managed, continuously monitored, and professionally led.
FAQ
Cybersecurity Risk Management FAQ
Effective cybersecurity risk management requires structure and consistency. Best practices include continuous monitoring across endpoints and cloud systems, disciplined vulnerability management, strong identity protection, and a documented incident response plan.
Organizations should align security measures to recognized security standards such as NIST or SOC 2. Regular vulnerability scanning reduces the attack surface. Clear reporting ensures executives understand the potential impact of cyber risks.
Start with a structured assessment of your attack surface. This includes evaluating:
- Existing security tools and their configuration
- Frequency and coverage of vulnerability scanning
- Patch management effectiveness
- Identity and privileged access controls
- Cloud configuration baselines
Next, map technical findings to business impact. Identify where vulnerabilities could result in data breaches, regulatory exposure, or service interruption.
A managed cybersecurity services partner can formalize this into an ongoing cybersecurity risk management program rather than a one-time review.
Effective cyber risk management relies on integrated tools, not isolated products. Core components typically include:
- Endpoint detection and response platforms
- Continuous monitoring systems
- Vulnerability scanning solutions
- Identity and access management controls
- Security information and event management platforms
However, tools alone do not reduce risk. Configuration, governance, and expert oversight determine effectiveness.
Traditional risk management often evaluates financial, operational, or market exposure at a high level. Cybersecurity risk management focuses specifically on threats to information systems, digital infrastructure, and data integrity.
It requires technical controls such as vulnerability management, identity protection, and continuous monitoring. It also demands faster response cycles due to the speed of security incidents.
Unlike traditional models that rely on periodic review, cybersecurity risk management operates continuously. It combines technical oversight with executive reporting to reduce breach probability and limit the potential impact of data breaches or regulatory violations.