Cloud Application Security
Protect the Cloud Platforms Your Business Depends On
RedZone does not simply support cloud infrastructure.
We operate the environment as a secure platform with measurable security posture, documented controls, and continuous operational assurance.
Pinpoint the Hidden Gaps in Your Cloud Environment
Cloud platforms and modern application architectures improve delivery speed, but they also expand the attack surface. Without structured oversight, cloud environments introduce security risks that are difficult to detect and control. RedZone approaches cloud application security as an operational responsibility. We create a stable environment where security controls actively mitigate security issues and risks.
With us at the helm, you'll gain:
- Reduced exposure to security incidents
- Predictable identity and access governance
- Early detection of suspicious activity
- Stronger audit and compliance position
The Results of Continuous Cloud Security Oversight
When cloud and application environments are governed correctly, organizations gain stable and defensible infrastructure.
RedZone applies structured application security in the cloud practices that detect risks early and maintain operational oversight.
Trusted by Organizations That Can't Afford Risk
Trusted by Organizations That Can't Afford Risk
“I want to thank you for supporting us last night with our emergency. You deployed your "A-Team" and it is refreshing to have a vendor respond with a sense of urgency and resourcefulness. Our IT manager said that RedZone was 'just awesome.'”
“When the NFL required every team in the league to do a Security Risk Assessment, we chose RedZone. Their Security Scoreboard gives my department all the technical information we need, while still displaying the data in a way our board can understand. It's unlike anything else on the market.”
Our Cloud Security Services
Cloud-Native Application Security: The RedZone Model
Security starts with architecture. Cloud environments must be designed with controlled identity access, segmented networks, and secure infrastructure baselines.
- Azure secure architecture and landing zones
- Network segmentation and workload isolation
- Secure cloud configuration baselines
- Microsoft Defender security platform integration
- Identity architecture using Microsoft Entra ID
Applications, APIs, and services expand the attack surface in application security in the cloud environments. We apply structured controls that govern how applications authenticate and store data.
- Application access and identity controls
- API authentication and security governance
- Application monitoring and activity logging
- DevOps security governance for CI/CD pipelines
- Application vulnerability assessment and remediation
Cloud environments change continuously. We maintain operational oversight through monitoring, posture management, and structured incident response.
- Cloud security posture management (CSPM) monitoring
- Identity activity monitoring and access review
- Security monitoring and centralized logging
- Incident response investigation and containment
- Continuous vulnerability management and remediation
Security-Led Operating Model
Most MSPs prioritize uptime and support delivery. We operate with security as the primary design principle.
Infrastructure, identities, and applications are governed through defined controls and monitoring processes. This reduces the likelihood of security incidents.
Ongoing Compliance Management
Regulated organizations must demonstrate control over infrastructure, data access, and security operations.
We integrate monitoring, vulnerability management, and evidence tracking with compliance frameworks. This reduces the effort required to prepare for regulatory audits.
Expert Security Oversight
The average MSP reviews cloud security periodically. We maintain continuous oversight of configuration, identity activity, and application exposure.
Through structured cloud security posture management (CSPM) and monitoring, risks are detected earlier and addressed before they escalate into operational issues.
The RedZone Approach: Security-First Cloud Operations
Our Technology Partners




























Where Cloud Application Security Becomes Critical
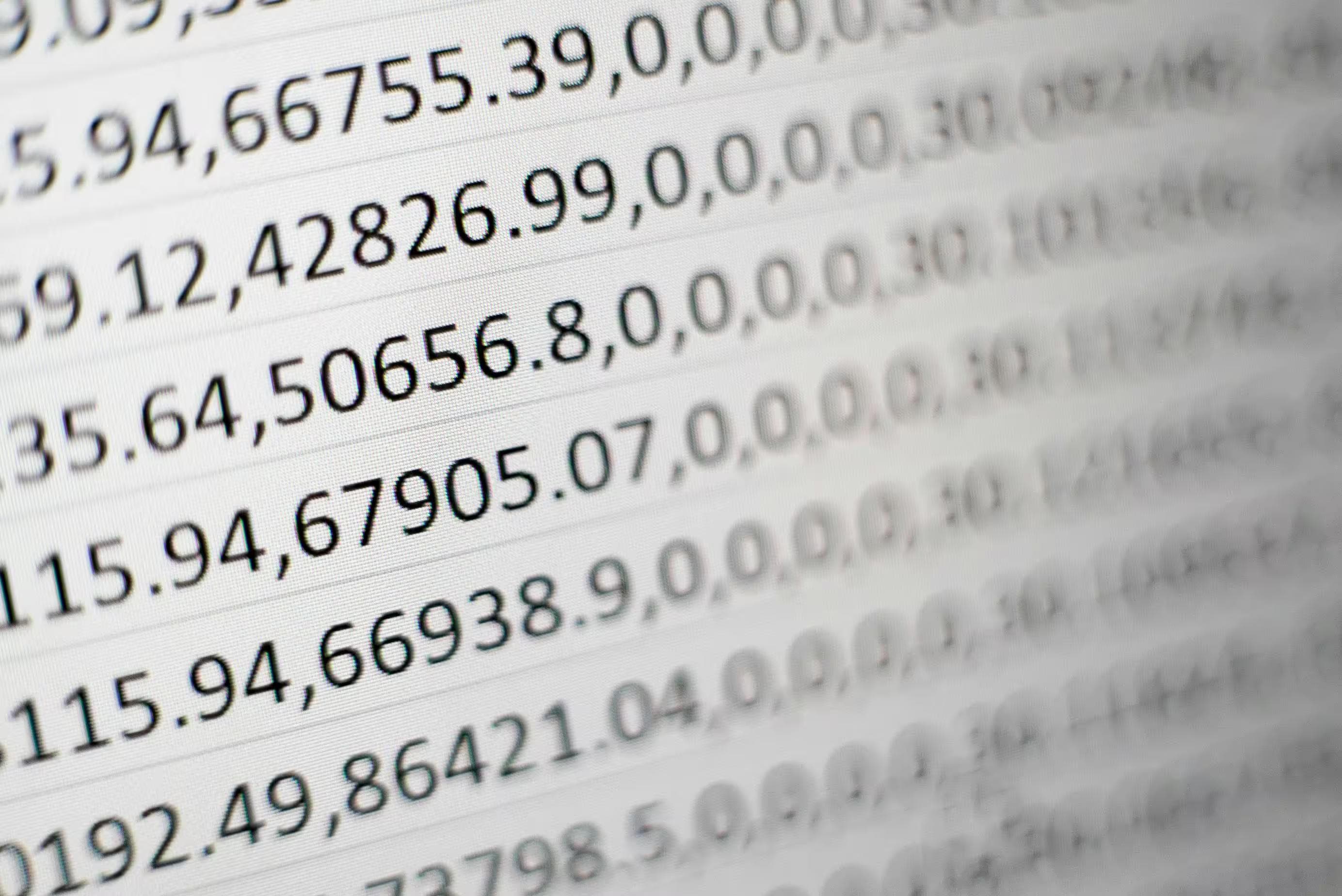
Organizations typically require structured application security in the cloud when their environments combine distributed platforms, sensitive data, and complex identity systems.
These conditions increase attack surface security risks and require continuous monitoring and governance.

Azure and Microsoft 365 Cloud Environments
Supporting core business systems and data

Cloud-Native Applications
Built on APIs, microservices, or containerized workloads
Identity-Heavy Environments
With large numbers of users, service accounts, and integrations
Multi-Application SaaS Ecosystems
Where data moves across cloud platforms
Organizations Handling Regulated or Sensitive Data
Requiring documented security controls
Rapidly Growing Cloud Environments
Where services, users, and permissions expand quickly
Secure Cloud Platforms and Apps the RedZone Way
In cloud environments, security cannot rely on periodic reviews or isolated tools. It requires structured oversight, disciplined architecture, and continuous operational control.
That control is central to the RedZone.
As a security-led managed services platform, we assume responsibility for the security posture of the entire cloud environment. Infrastructure architecture, identity governance, monitoring, and compliance oversight operate together through a unified operating model.
Our model ensures cloud platforms remain stable, controlled, and accountable.
Cloud Application Security FAQ
Effective application security in the cloud requires structured controls across infrastructure, identities, and applications. Best practices include enforcing strong identity and access management (IAM), protecting APIs, applying secure cloud architecture, and maintaining continuous monitoring through cloud security posture management (CSPM).
Organizations should also implement vulnerability management, centralized logging, and defined incident response procedures to address emerging security issues quickly.
Organizations protect cloud-native application security environments by controlling identity access, securing APIs, and monitoring application activity continuously. Security monitoring and threat detection help identify abnormal behavior early.
Businesses should also govern SaaS usage through cloud access security broker (CASB) capabilities and regularly review infrastructure configurations to reduce attack surface security risks.
Protecting cloud-based application security environments requires ongoing vulnerability management across both infrastructure and applications. This includes regular vulnerability scanning, patch governance, secure API authentication, and monitoring for configuration weaknesses.
Continuous oversight of cloud platforms through CSPM helps detect exposure before it leads to cloud service data breaches.
Application security in cloud computing environments is critical because applications, APIs, and identity systems form the primary entry points into cloud platforms.
Weak access controls, exposed APIs, or misconfigured services can quickly lead to security incidents or data exposure. Strong cloud application security ensures that applications, identities, and data remain protected while operating across distributed cloud services.
Organizations implement application security in the cloud by combining secure architecture, identity governance, and continuous monitoring. This includes enforcing IAM policies, securing APIs, integrating logging and threat detection, and maintaining continuous CSPM.
When these controls operate together, organizations can continuously monitor cloud security posture and respond quickly to emerging risks.